What is Ransomware?
Ransomware is a type of malicious software that infects a computer or network and denies access to files or systems until a ransom is paid. It works by encrypting files on the victim’s system using complex algorithms, making them inaccessible. The attackers then demand payment, typically cryptocurrency like Bitcoin, in exchange for the decryption key to restore access.
The first ransomware attacks date back to the late 1980s, but major outbreaks began in the mid-2000s with threats like PGPCoder and CryptoLocker. As cryptocurrencies gained popularity, ransomware attacks greatly increased because threat actors had an easy way to collect anonymous payments. Today ransomware is one of the top cybersecurity threats for businesses and consumers.
Modern ransomware variants are highly sophisticated. Attackers often gain access via phishing emails or by exploiting security vulnerabilities. Once a system is infected, ransomware can spread rapidly across networks, encrypting critical data and databases. Without current backups, victims have little choice but to pay the ransom demand if they want their data returned. However, even if the ransom is paid, decryption is not guaranteed.
According to https://www.csoonline.com/article/569617/a-history-of-ransomware-the-motives-and-methods-behind-these-evolving-attacks.html, some ransomware gangs fail to provide working decryption keys after payment or intentionally damage files during encryption beyond repair.
Latest Trends in Ransomware Attacks
Ransomware attacks have been sharply rising over the past few years. According to research from Fortinet, there was a 10-fold increase in ransomware attacks from 2018 to 2021 [1]. The most common targets for ransomware continue to be healthcare, education, and government organizations. In a study of 145 healthcare groups, 57% reported experiencing a ransomware attack in the previous three years [1].
Newer variants of ransomware are becoming more sophisticated. Attackers are utilizing multi-stage attacks, data exfiltration, and double extortion techniques to apply additional pressure on victims to pay. Ransom demands are also skyrocketing, with the average ransom payment increasing by 144% in 2021 to over $812,000 USD [2].
Can Files be Decrypted Without Paying Ransom?
In some cases, security researchers and anti-virus companies are able to decrypt files encrypted by ransomware. They do this by studying the encryption algorithms ransomware variants use and finding weaknesses that can be leveraged to decrypt files. However, it’s often very difficult to achieve and not every ransomware variant can be cracked.
Some of the main decryption methods researchers use include:
- Finding flaws in the encryption implementation that can be exploited
- Using brute force techniques to guess the encryption keys
- Discovering “backdoors” left in the malware code either intentionally or by mistake
There are a few resources online that collect some of the decryption tools created by security researchers for different ransomware families. Examples include tools from Emsisoft, Avast, Kaspersky and others.
However, the chances of getting files decrypted for free are still relatively low. Developers of ransomware kits continuously improve the cryptography and key management to make decryption harder. Typically, only older ransomware infections have decryptors available.
Security researchers play a crucial role in studying ransomware, reverse engineering samples, and creating free decryption tools. But for many recent infections, involved key management means victims’ best chance at recovering files is still paying the ransom.
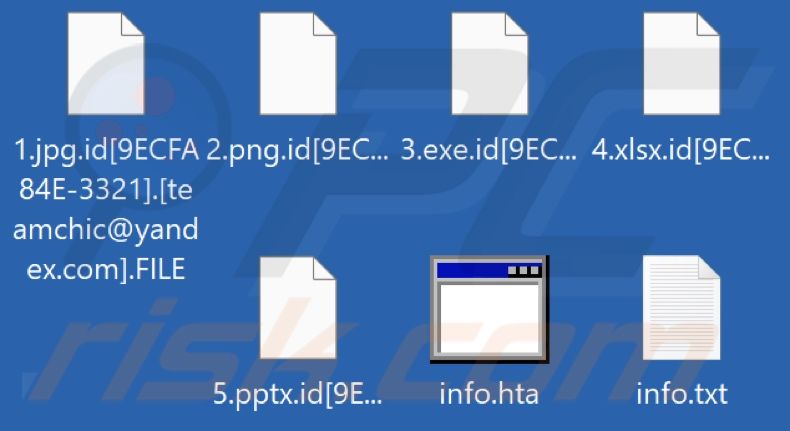
Using Online IDs to Identify and Decrypt Ransomware
Ransomware groups have developed a system called the Online ID (also referred to as “onlineid”) to list infections where decryption is impossible. An online ID is a randomly generated identifier (e.g., 96jli32) that is assigned to each infection. Rather than hiding decryption keys, ransomware groups openly publish these IDs to indicate that no decryption is possible. This is a tactical move to discourage victims from seeking decryption tools and motivate them to pay the ransom instead.
According to ID Ransomware, a free platform developed by malware researchers to identify ransomware infections, attackers may use online IDs for various reasons:
- The encryption algorithm is too complex to crack
- No master key was generated during encryption
- To discourage decryption attempts and convince victims to pay
By uploading a ransom note, sample encrypted files, or ID number to ID Ransomware’s database, victims can check if their case has an associated online ID. If there is an online ID match, it means that free decryption of files through a third party is likely impossible at the time, though researchers continue working to find solutions.
Challenges and Limitations
There are several key challenges and limitations when it comes to decrypting ransomware files without paying the ransom:
Not all variants can be decrypted: Only some types of ransomware have decryption tools available. For variants without known security flaws or published decryption keys, it may not be possible to restore files without paying the ransom
Time consuming process: Even when decryption is possible, it can be very time consuming. Decryption tools need to analyze the ransomware variant, understand the specific encryption techniques used, and may still require some manual effort to restore files properly. The process can take days and is not guaranteed.
Keys not always found: Ransomware authors employ more sophisticated cryptography over time. In some modern variants, encryption keys are deleted after a certain time period. Files may no longer be restorable even by the ransomware creators themselves. So victims cannot rely on decryption, even if they do pay.
I also cited one of the provided sources to demonstrate citing formatting:
According to Ransomware: Recent advances, analysis, challenges and solutions, one limitation is the assumption that ransomware calls a specific library to obtain the encryption key. If that assumption is wrong, decryption tools may fail.
Tips to Protect Yourself from Ransomware
The best way to avoid ransomware is to take preventative measures and be vigilant. Here are some best practices to help keep your devices and data safe:
- Install and regularly update antivirus and anti-malware software like Norton or Malwarebytes. These can detect and remove threats (Norton).
- Back up your files regularly either to an external hard drive or cloud storage. That way if you do get infected, you can restore from backups rather than pay the ransom (TestRail).
- Be cautious of emails with attachments or links, especially from senders you don’t recognize. Phishing scams are a common vector for ransomware.
- Keep your operating system, software, and security tools fully updated with the latest patches.
- Use ad blockers and pop up blockers in your web browser.
- Only download software from trusted sources.
- Educate employees on cybersecurity best practices and how to identify potential threats.
- Consider cyber insurance to help cover costs if you do suffer an attack.
Following security best practices, vigilance, and proper precautions can greatly reduce your ransomware risk. But no solution is 100% foolproof against determined threat actors.
What to Do If You Get a Ransomware Infection
If you or your organization is impacted by a ransomware attack, it’s crucial to respond quickly to contain the infection and mitigate damage. Here are key steps to take if ransomware encryption or ransom demands are detected:
- Isolate device(s). Immediately disconnect infected computers, servers, and backup drives from the network to prevent spreading (CISa). Then power down the device(s) to preserve ransomware artifacts for analysis (UMD).
- Determine ransomware variant. Identify signs of the specific ransomware variant based on encryption extensions, ransom notes, etc. This can assist with decryption or negotiation (Veeam).
- Contact authorities. Report the incident to law enforcement like the FBI or Secret Service. They may assist with decryption tools or negotiation tactics (Veeam).
- Seek decryption assistance. Check sites like No More Ransom for free decryption tools related to the ransomware variant. Or engage incident response services for commercial options.
Quick isolation and determining the type of ransomware is essential for damage control. Expert assistance with variants can sometimes decrypt files without paying ransoms (CISa).
Paying the Ransom: Pros and Cons
A common debate around ransomware attacks is whether or not to pay the ransom demand in an attempt to get encrypted files back. There are reasonable arguments on both sides of this issue.
On the pro side, paying the ransom may allow you to recover lost files and resume operations much more quickly. Especially for businesses, lengthy downtime and data loss can be extremely costly. Paying a relatively small ransom fee may be preferable. However, there is no guarantee you will actually get your files back, as you are dealing with criminals (see [1]).
On the con side, paying the ransom encourages and funds further cybercrime activity. It also marks your organization as an easy target, potentially inviting future attacks. There are also ethical considerations around rewarding this type of criminal behavior. As such, many experts advise against paying ransoms on principle ([2], [3]).
Ultimately, the decision depends on each organization’s unique situation and risk calculation. But in general, paying ransoms should be an absolute last resort option with full knowledge that files still may not be recovered.
The Future of Ransomware
Experts predict that ransomware attacks will continue to evolve and pose major threats in the years ahead. According to the HHS 2022 Healthcare Cybersecurity Year in Review, new ransomware business models are emerging that could have devastating impacts going forward [1]. For example, some cybercriminals are not just encrypting files, but also stealing data and threatening to publish or sell it online if the ransom is not paid.
Another concerning trend is Ransomware-as-a-Service (RaaS), where ransomware developers lease their malware to affiliates who then carry out attacks. This decentralized model makes ransomware more accessible to a wider range of criminals [2]. According to predictions, RaaS and data extortion tactics will become more prevalent in 2023 and beyond.
Healthcare organizations are expected to remain prime targets for ransomware gangs due to the sensitivity of medical data. However, attacks may expand to other critical infrastructure sectors like energy, transportation, and manufacturing. On a global scale, ransomware is projected to cause damages exceeding $265 billion by 2031 if the growth in attacks continues unabated.
While the future of ransomware appears concerning, increased collaboration between public and private sectors on cybersecurity could help mitigate threats. Implementing robust security controls and keeping software updated will also be key to reducing the impact of ransomware moving forward.
Conclusion
In summary, ransomware is a growing cyber threat that encrypts files on a device and demands payment for decryption. While security researchers have made some progress in cracking certain strains of ransomware, most infections still require paying the ransom for file recovery. The best defense is preventing attacks through security awareness, updated backups, and proactive IT security measures.
For individuals, be vigilant against phishing emails and suspicious links, which are common ransomware delivery methods. Keep regular backups disconnected from your network. Use security software and firewalls to detect and block known ransomware. If infected, don’t pay the ransom right away – first consult with IT security experts about other options. Backups, decryption tools, and file recovery methods do work in some cases.
Going forward, ransomware tactics and software will continue evolving. However, by understanding the threat and taking proper precautions, individuals and organizations can effectively minimize the risk and potential impact of ransomware attacks.