Locky ransomware is a type of malicious software that encrypts files on a victim’s computer and demands a ransom payment in order to decrypt the files. It has been one of the most widespread and destructive ransomware variants in recent years.
What does Locky ransomware do?
When activated, Locky ransomware will encrypt hundreds of different file types on local drives and mapped network drives associated with the infected computer. It utilizes strong encryption algorithms, so files that get encrypted are completely inaccessible. Locky appends the .locky extension to all encrypted files.
Once encryption is completed, Locky ransomware will display a ransom note in a text file. This note informs the victim that files have been encrypted and demands a payment of between 0.5 and 1 bitcoin (around $400-$800 at current exchange rates) within a short timeframe. It provides instructions on how to purchase bitcoin and send the payment. The note warns that if payment is not received in time, the decryption key will be destroyed and files will remain locked forever.
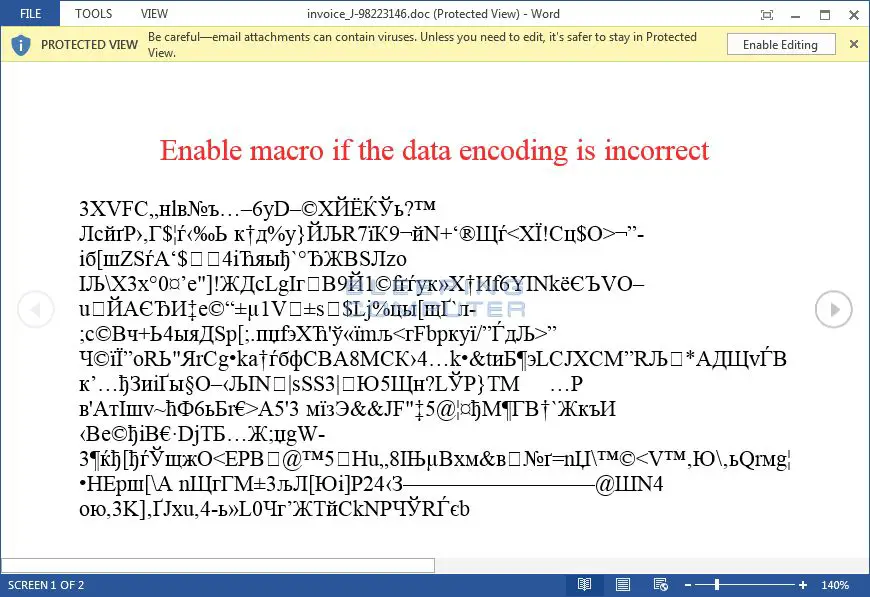
Locky ransomware is distributed through spam email campaigns that deliver malicious Word documents containing macros. When opened, these macros download and install the Locky malware. Early versions required the user to enable macros, but later campaigns used exploits to bypass this requirement and install automatically. The emails often pose as invoices, order confirmations, or other communication from a legitimate organization to fool the recipient into opening the attached document.
What are some examples of how Locky infects systems?
Here are some common infection methods used by Locky ransomware campaigns over the years:
- Malicious Word document attachments in spam emails – Emails pretend to be invoices or other files, users instructed to “enable macros” which downloads Locky.
- Infected PDF attachments – PDFs instruct users to click a link to view content, the site downloads Locky.
- Malvertising – Locky code installed on ad networks serves ads that download Locky onto visitor computers.
- exploit kits- Sites with exploit kits probe for browser vulnerabilities, push Locky install if found.
- Remote Desktop Protocol (RDP) – Brute force attacks on RDP logins deploy Locky once access gained.
- Software bundles – Locky bundled covertly with some “free” software downloads.
- Fake apps – Fake versions of apps like PokemonGo infected with Locky.
In most cases, the infection process is triggered by a user action such as opening a malicious attachment, clicking a link, or downloading software. Advanced social engineering and exploits are used to initiate the infection without the user realizing malicious code is being installed.
What are the effects of Locky ransomware?
The main effects of a Locky infection include:
- Encryption of a wide range of important files across local and networked drives.
- Disruption to business processes that rely on access to encrypted files.
- Loss of access to personal documents, photos, databases, and other data.
- Extortion through ransom payment demands of $400-$800 in bitcoin.
- Revenue generation for cybercriminal networks through ransom payments.
- Costs related to response, investigation, remediation, and rebuilding systems.
- Reputational damage and loss of customer trust if data is leaked.
The effects can be severe for businesses in particular. When documents, databases, financial files and other corporate data is encrypted, workflow grinds to a halt. The interruption to operations can be very costly to organizations.
What is the impact of paying the ransom?
If the ransom is paid, cybercriminals will provide instructions on how to obtain a private decryption key. This key can then be used by victims to unlock and recover their files by running a decryption tool.
However, there are several risks involved with paying the ransom:
- There is no guarantee files will be recovered – criminals may not provide working decryption.
- Paying the ransom funds and enables future cybercrime.
- It identifies the victim as someone willing to pay, which may lead to further attacks.
- Ransom payments can violate legal restrictions against supporting criminal entities.
- Decryption tools can have bugs and cause data damage or loss.
- Ransom demands may increase if criminals know the victim will pay.
Many cybersecurity experts advise against paying ransoms for these reasons. There are often other options available for file recovery that don’t carry these additional risks.
What options exist for recovering encrypted files without paying ransom?
Some methods that may work for recovering encrypted files without paying cybercriminals include:
- File backups – Restore files from clean backups made before infection.
- Cloud storage – Sync services may have old copies of files stored online.
- Shadow copies – Restore previous versions of files from system restore points.
- Decryption tools – Some free decryption tools exist released after ransomware cracks.
- Malware analysis – Analysts may extract decryption keys from malware code samples.
- Format and reinstall – As a last resort, wipe systems and reinstall software.
The most reliable method is having clean, recent backups available that are isolated from the network where ransomware would not be able to infect them. Regular offline backups are the best defense against permanent data loss.
What tips can protect against Locky infections?
Here are some best practices that can be followed to avoid Locky ransomware attacks:
- Train employees to identify social engineering techniques and suspicious emails.
- Scan all incoming email attachments with antivirus software.
- Block macros from running automatically in Office documents.
- Enable spam filters and scan outbound network traffic for anomalies.
- Patch software like Java, Flash, browsers to eliminate exploit vectors.
- Use pop-up blockers and ad blockers while web browsing.
- Maintain backups offline and regularly test restores.
- Segment networks and use a DMZ architecture to contain outbreaks.
- Restrict administrator privileges on user workstations.
- Deploy endpoint detection and response tools to block malicious processes.
Layered defenses across users, networks and endpoints are key to preventing ransomware like Locky from infecting systems and encrypting critical data.
How was Locky ransomware created? Who is behind it?
Locky ransomware first appeared in early 2016. Researchers attribute it to an organized cybercriminal gang thought to be based somewhere in Eastern Europe. This threat actor group is believed to be involved in many ransomware variants including Dridex, Zeus and Pony.
Locky has been distributed via spam campaigns that rely on compromised business email accounts and malvertising to infect users. The actors behind it operate an affiliate model, utilizing a ransomware-as-a-service approach to scale up attacks. The developers sell or rent their malware to other criminals, then get a cut of any ransom payments.
This ransomware tool is constantly tweaked and rebranded, with variants like Lukitus, Diablo6, Locker, and Thor appearing in the years since. But researchers identify the same criminal gang behind Locky creating or reusing code for many ransomware families. Their technical sophistication and criminal infrastructure have allowed them to remain active and evade authorities.
How does Locky ransomware encrypt files? What encryption does it use?
Locky uses a technique called asymmetric or hybrid encryption to scramble data. Both RSA and AES encryption algorithms are used in the process:
- The RSA public-private key pair is generated. The public key is distributed while the private key is stored on the attacker’s command and control server.
- A unique AES symmetric key is generated to encrypt each file. AES offers high speed but the key must be transmitted.
- The AES key for a file is encrypted with the RSA public key before it is sent to encrypt the target file.
- The file is encrypted using that AES encrypted key, with AES in CBC mode and 128 bit blocks.
- The encrypted AES key is saved in the file header so the RSA private key can decrypt it to decrypt the file.
This complex process chains the high speed of AES with the key exchange abilities of RSA public-key cryptography. Without the RSA private key to decrypt the AES encryption keys, the files remain locked. The private key is controlled by the ransomware operator only.
What is the typical ransom payment demand for Locky ransomware?
The ransom payment demanded by Locky is usually between 0.5 and 1 bitcoin. At the November 2022 exchange rate, this equals approximately:
- 0.5 BTC = $9,500 USD
- 1.0 BTC = $19,000 USD
However, earlier variants from 2016 demanded payment ranging from 0.5 to 4 bitcoins, up to around $800 at the time. Some later versions asked for payment in Dash cryptocurrency instead.
The ransom notes threaten permanent file loss if payment is not made quickly, typically within 72 or 96 hours from infection. Some Locky notes try to increase urgency with threatening language, fake FBI warnings, or claims that payment doubles after the deadline.
In most cases the cybercriminals will extend the deadline and negotiate the ransom amount if contacted. Paying anything does not guarantee files can be recovered. The victim is dependent on receiving a valid decryption tool.
What is the decryption tool for Locky ransomware? How does it unlock files?
The decryption tool provided for Locky is essentially an application that takes encrypted files and the RSA private key as input. It extracts the AES encryption key from the file headers using the RSA key. These AES keys are then able to decrypt the files back into a usable form.
Without access to the RSA private key held by the attackers, the tool cannot retrieve the AES keys required to decrypt files. This key is necessary to unlock files along with the decryptor. Some free decryption tools have been created by security firms when vulnerabilities are found in old ransomware samples. But newer Locky variants utilize improved cryptography to prevent decryption.
Are there any known weaknesses that allow Locky to be decrypted without paying?
Some weaknesses have existed in past ransomware variants that enabled decryption without paying ransom:
- Poorly generated encryption keys – Allowed keys to be predicted.
- Hard-coded keys – Keys reused across infections.
- Cryptographic flaws – Vulnerabilities in old ciphers.
- Flaws in key storage – Ability to extract keys from memory.
- Recovery of the key server database – Access to stored keys.
However, the developers behind Locky have proven adept at patching any vulnerabilities uncovered and improving their encryption implementations. Some decryption tools for old variants may exist, but newer Locky ransoms typically cannot be decrypted without obtaining the RSA private key from the ransomware operators.
Free decryption is not possible in most cases. Thorough backup protocols offer the best chance of file recovery without paying the ransom.
What are some famous examples of Locky ransomware attacks?
Some notable victims of major Locky ransomware attacks include:
- Hollywood Presbyterian Medical Center – Paid $17,000 ransom in Bitcoin in 2016.
- University of Calgary – Paid $20,000 ransom to unlock campus systems in 2016.
- ERIE County Medical Center – 6,000 computers encrypted, causing major disruption.
- New Bedford City Hall – Entire city government network disabled by attack.
- Los Angeles Valley College – 5,000 computers encrypted, two months to recover.
These examples illustrate how wide-ranging the damage from ransomware can be. Large organizations are prime targets that have difficulty functioning when files are encrypted across their entire infrastructure. Cybercriminals exploit this disruption to demand large ransoms.
Conclusion
Locky demonstrated just how debilitating ransomware could be when it first appeared in 2016. Utilizing stealthy distribution and strong encryption, Locky allowed cybercriminals to extort businesses and institutions by cutting off access to their data. It exemplified the rise of ransomware as a lucrative endeavor for malware developers.
The criminal syndicate behind Locky continues to innovate and release new variants to this day. Their ransomware-as-a-service model provides the infrastructure to scale attacks exponentially. Defending against ransomware threats like Locky requires ongoing vigilance – backing up critical data, hardening security policies, training employees, and deploying advanced endpoint protection.