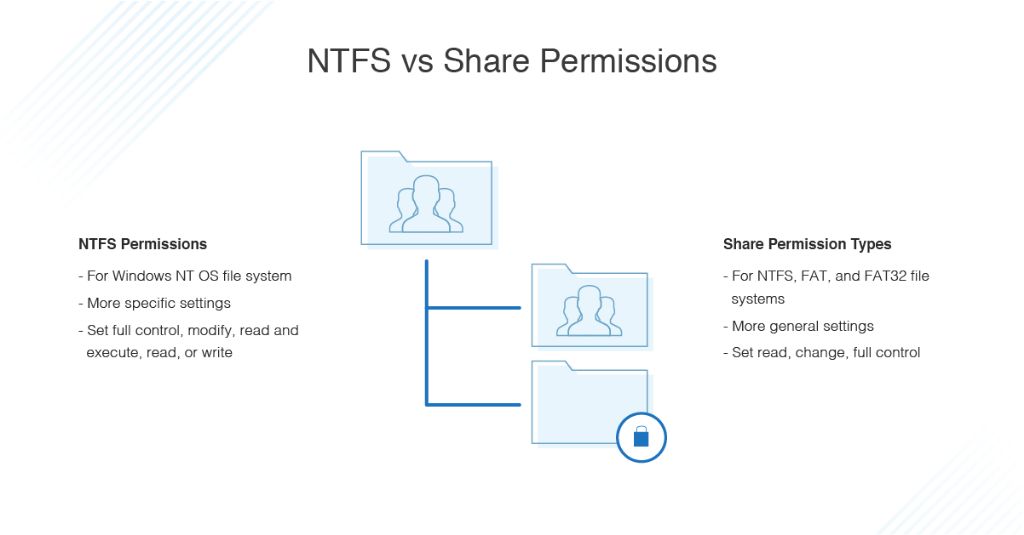
NTFS permissions and share permissions are both important concepts in managing file system security on Windows networks. NTFS permissions control access to files and folders on an NTFS volume at the file system level, while share permissions control access when folders are shared over the network. Understanding the differences between these two permission systems is crucial for properly securing resources and avoiding permissions issues.
File permissions in general serve a vital purpose in computing and networking. As explained on Hackernoon, “I just want to show the importance of file permissions to normal people. Many organizations will have an IT department or even an outside company dedicated to setting up and maintaining permissions to keep data secure.”
Properly configuring NTFS and share permissions is key to restricting unauthorized access to sensitive data. As Ravindra P states on LinkedIn, “File permissions are crucial for several reasons: Security: File permissions ensure that only authorized users and processes can access files and folders.”
NTFS Permissions
NTFS (New Technology File System) permissions control access to files and folders on NTFS volumes. They are used to manage data stored on hard drives formatted with NTFS. NTFS permissions apply to users and groups on the local computer where the NTFS volume resides.
Some basic NTFS permissions include:
- Read – Allows viewing and opening files and folders
- Write – Allows modifying, deleting, creating files and folders
- Full Control – Allows full access to create, delete, modify files/folders and their properties
NTFS permissions are specified at the file and folder level and control what actions permitted users can take. Permissions can be allowed or denied for individual users or groups. By default, permissions are inherited from parent folders unless explicitly specified.
NTFS permissions provide granular control over file and folder access on local NTFS volumes. They allow administrators to configure access rights based on user accounts and groups.
Share Permissions
Share permissions determine the access users have when connecting to shared folders and files over a network. They specify the level of access a user has when accessing the share via the network path (e.g. \\server\share).
Share permissions apply to anyone accessing the share over the network, including authenticated domain users, guest users, and anonymous users. They do not apply to users accessing the files locally on the server itself.
Some common share permissions include:
- Read – Allows viewing and listing files and folders in the share
- Change – Allows modifying existing files and folders
- Full Control – Allows full access to create, modify, and delete files and folders
Share permissions are used to control basic network access to a shared resource. More granular file and folder permissions can be specified using NTFS permissions.
To view and configure share permissions in Windows, the Share tab can be used in the file/folder Properties dialog box.
Key Differences
The key difference between NTFS permissions and share permissions is that NTFS permissions operate at the file system level, while share permissions operate at the share level. NTFS permissions control access to files and folders on a local NTFS volume, while share permissions control access to shared folders across a network.
Some specific differences include:
- NTFS permissions are set on the file system and define what a user can do with a file or folder on a local volume. Share permissions are set on a shared folder and define what a user can do to that folder over the network.
- NTFS permissions provide more granular control as they can be set separately on files and folders. Share permissions apply to the entire share.
- NTFS permissions affect all local users on a system. Share permissions only affect users accessing the share over the network.
- By default, NTFS permissions are inherited from parent folders. Share permissions do not inherit by default.
In summary, NTFS permissions control local access while share permissions control network access. NTFS permissions are more granular, while share permissions operate at the share level. Both can be used together to provide comprehensive access control.
Inheritance
One key difference between NTFS permissions and share permissions is that NTFS permissions support inheritance, while share permissions do not. With NTFS permissions, child objects like subfolders and files inherit permissions from their parent folder by default. So if you grant the Sales group Modify permissions to the Sales folder, new subfolders and files in the Sales folder will inherit those permissions automatically. This allows administrators to set permissions on parent folders and have those permissions propagate down the directory tree, rather than having to manually configure permissions on every single subfolder and file. [1]
Share permissions do not have this inheritance capability – permissions set on the share do not flow down to child objects. Every subfolder and file must have share permissions configured individually. Given the number of objects in a typical file system, configuring share permissions in this way would be extremely tedious. The inheritance model with NTFS permissions makes setting and managing permissions much easier. [2]
It’s important to understand how inheritance works with NTFS permissions. By default, child objects inherit permissions, but inheritance can be disabled to block permissions from flowing down. Administrators can also choose to replace inherited permissions on child objects with new unique permissions. So even with inheritance, NTFS permissions can be tailored at each level of the directory tree.
Precedence
Both NTFS permissions and share permissions restrict access to shared files and folders, but NTFS permissions take precedence over share permissions. If there is a conflict between the two, the most restrictive permission will apply. For example, if NTFS allows read access to a file but the share permission only allows read access to some users, those users will not be able to access the file even though NTFS permits it. This is because NTFS permissions override the less restrictive share permissions.
The reason NTFS permissions take precedence is that they operate at a lower level, directly controlling access to files and folders on the NTFS volume. Share permissions are higher level and apply to the entire share. So if a resource has both NTFS and share permissions defined, the more restrictive NTFS permissions will be enforced over the share permissions. Generally it is recommended to leverage NTFS permissions as the primary access control mechanism as they offer greater granularity.
According to Varonis, “Share permissions override NTFS permissions only when the Share permission is more restrictive than the NTFS permission.” In summary, NTFS permissions take precedence unless the share permission is more restrictive, in which case the share permission will be enforced.
Managing Permissions
Best practices for managing NTFS and share permissions focus on using groups instead of individual user accounts. The two main tools for managing permissions are:
- File Explorer – provides a GUI for managing NTFS permissions on folders and files. Best practices are to assign permissions to groups rather than individual accounts for easier management.
- Share Permissions tab – located in a share’s Properties window, this tab allows configuring share permissions. Best practices are to give the Everyone group Full Control and rely on NTFS permissions for more granular access control.
Additional tools like icacls and PowerShell can help automate permission changes across many files and folders. Overall best practices are to leverage groups, rely on NTFS permissions over share permissions, and avoid assigning individuals Full Control.
Troubleshooting
There are a few steps you can take to diagnose NTFS and share permission issues:
First, check the access denied messages when trying to access files or folders. These messages usually indicate whether it’s a share permission or NTFS permission causing the issue. For example, “Access is denied” generally points to NTFS permissions, while “You do not have permission to access” suggests share permissions are misconfigured.
You can also use tools like the Effective Permissions tab in file or folder Properties to view effective versus directly applied permissions. The Effective Access view in Windows Security shows effective permissions from group memberships.
Comparing effective versus directly assigned permissions helps uncover conflicts.
Additionally, enabling debug logging for permission issues can provide useful troubleshooting information. You can find debugging tools under Local Group Policy Editor > Computer Configuration > Administrative Templates > System > Troubleshooting and Diagnostics.
As a last resort, completely resetting permissions may be required. Back up data first, then use the tool ResetPerms.exe or TakeOwn.exe to wipe all permissions and start fresh.
See this guide for steps on diagnosing permission issues: Configure and troubleshoot NTFS permissions
Security Considerations
When assigning NTFS and Share permissions it is important to follow the principle of least privilege. Users should only be granted the permissions they need to perform their job duties and no more. Assigning excessive permissions increases the risk of data breaches and malware infections. One best practice is to avoid granting users full control permissions whenever possible.
It is also crucial to periodically review permissions to ensure they are still appropriate as user roles change over time. According to ManageEngine, “Unused, excessive permissions open security holes that can be exploited by disgruntled employees, malicious insiders, and crafty hackers.” Regularly auditing permissions allows you to remove unnecessary access and reduce your attack surface.
Overall, following least privilege principles, conducting periodic reviews, and granting only required permissions is essential for securing your environment. Proper permissions configuration is a fundamental aspect of data security and risk management.
Conclusion
In summary, the key differences between NTFS permissions and share permissions are:
- NTFS permissions apply to the local file system, while share permissions apply to network access
- NTFS permissions provide more granular control, as share permissions have a more limited set of options
- Share permissions provide a separate layer of security for network access
- NTFS permissions are inherited by subfolders and files, share permissions are not
- NTFS permissions take precedence over share permissions in most cases
Understanding how both NTFS and share permissions work together is critical for implementing proper security and access control. NTFS permissions secure the underlying files and folders, while share permissions add an additional layer for securing remote network access. Using both in tandem allows creating a robust permissions scheme to prevent unauthorized access.
When troubleshooting access denied errors, it’s important to check both the share and NTFS permissions. The interplay between inheriting permissions, precedence, and overlapping permissions can make troubleshooting complex. Learning best practices for applying secure but usable permission settings will help manage servers and file shares.