LockBit ransomware first appeared in September 2019 and has quickly become one of the most active and dangerous ransomware strains. But where did this prolific cyber threat originate from and who is behind it?
The Origins of LockBit
LockBit is believed to have first emerged out of Eastern Europe, likely from a Russian-speaking cybercriminal group. Some key points about its origins:
- The earliest version of LockBit (v1.0) contained Russian language artifacts, suggesting its authors were Russian speakers.
- Analysis of LockBit’s code indicates it is likely based on the Thanos ransomware code, which also originated from Eastern European cybercriminals.
- LockBit uses the Russian domain .ru for many of its operations, including for hosting data leak sites.
- The ransomware avoids encrypting systems that use languages associated with former Soviet states, hinting its creators want to avoid impact in that region.
Russia has a thriving cybercriminal ecosystem and is known to be a safe haven for some ransomware gangs, leading many experts to conclude LockBit has roots within Russian-speaking hacker groups.
The LockBit Ransomware-as-a-Service
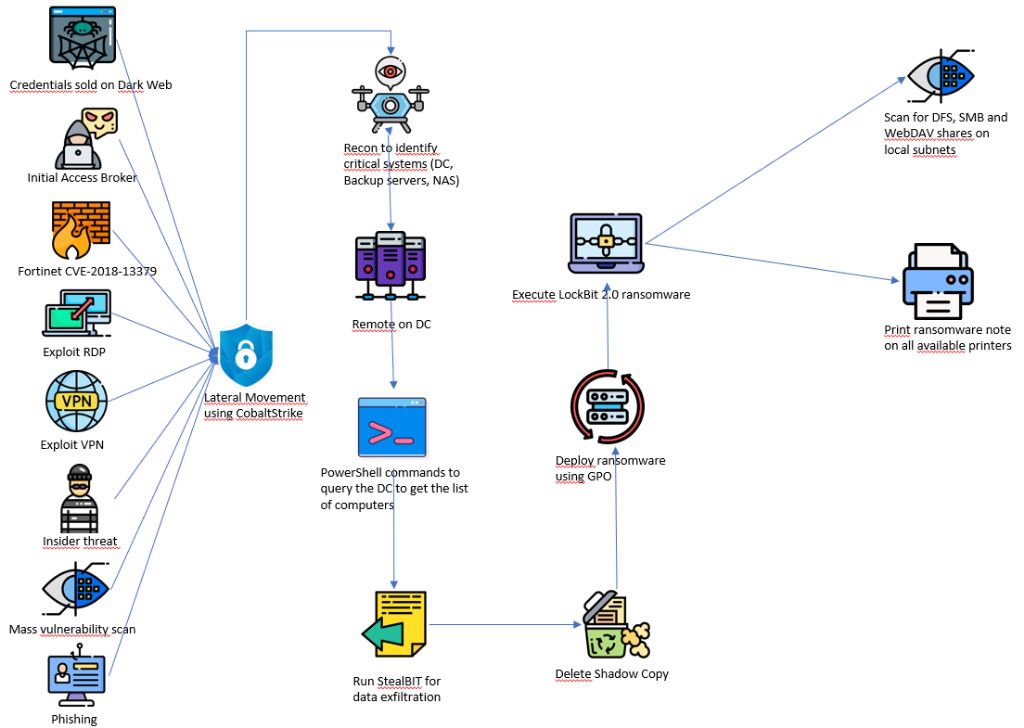
LockBit operates according to the Ransomware-as-a-Service (RaaS) business model. This means its developers maintain the malware code and infrastructure, then rent it out to “affiliates” who deploy the ransomware to victims. Key aspects of LockBit as a RaaS operation:
- Affiliates gain access to the malware via the dark web in exchange for a cut of any ransom payments.
- Developers handle tasks like negotiating with victims, collecting ransoms, data exfiltration and publicity.
- This decentralized structure allows rapid scalability, with affiliates conducting attacks worldwide.
- Having separate teams for development and deployment also helps LockBit evade law enforcement.
LockBit claims to vet affiliates, only selecting skilled hackers with proven experience running ransom operations. They provide extensive technical support and marketing resources to affiliates.
Where LockBit Operates From
While LockBit appears to have originated in Russia, its decentralized RaaS structure means the cybercriminals running it could be based anywhere globally. Some insights into their operations:
- Most LockBit affiliates are believed to operate out of Russia or other Eastern European and former Soviet nations.
- However, attacks have been conducted from IP addresses around the world, including North America, Western Europe, Asia and more.
- Communication from the LockBit developers often indicates they are based in Russia/Eastern Europe due to language use.
- Developers claim they will not attack victims in CIS countries, suggesting they want to avoid drawing attention in their homeland.
So in summary, while LockBit likely originated in Russia, its global affiliate structure means attacks can be run from virtually anywhere. But Russia and other former Soviet nations remain the primary base of operations.
The Human Operators Behind LockBit
Very little is definitively known about the human members behind the LockBit ransomware operation. Some details that have emerged:
- In early 2022, LockBit announced its leadership as a group called “LockBit Black” led by someone using the name “Diablo.”
- Diablo claims to have formed LockBit Black by recruiting experienced ransomware developers and hackers.
- The LockBit site lists 9 core team members with hacker handles, but their real identities remain unknown.
- Affiliates use pseudonyms and cryptocurrency to remain anonymous even to LockBit developers.
In summary, the individuals running LockBit remain unidentified. The decentralized, pseudonymous nature of their RaaS model makes pinpointing exact members difficult. But profiling suggests they are experienced cybercriminals based primarily in Russia or other Eastern European nations.
Location Insights from LockBit Cyber Attacks
Looking at patterns in LockBit’s many cyber attacks also provides clues into where its operators are based and from where attacks are staged. Some observations:
- Most ransomware deployments occur on weekends, indicating operators work normal weekday schedules.
- Attack patterns align with timezones in Russia/Eastern Europe, with little activity during those nighttime hours.
- English language communications sometimes contain grammatical errors indicating non-native speakers.
- Attacks target mainly Western countries, with very few incidents reported in Russia/former Soviet nations.
This activity analysis reinforces the assessment that most LockBit members reside in Russian or similar timezones, and avoid attacking targets within their homeland region.
Conclusion
Although it has grown into a massive, borderless ransomware operation, the evidence strongly indicates LockBit started out among Russian-speaking cybercriminals, most likely in Russia or another Eastern European nation. Its core developers appear to still be based in that region, although affiliates operate globally. The group’s growth into a RaaS model has expanded its reach while maintaining ties back to its origins among hacker groups in Russia and the former Soviet bloc.