Malware attacks have become increasingly common in recent years as cybercriminals look to steal data, money, and information from unsuspecting victims. Preventing malware attacks requires a multi-layered approach involving security awareness, software solutions, and safe computing practices.
What is malware?
Malware is any software that is designed to cause damage to a computer, server, client, or computer network. Malware includes viruses, worms, trojans, ransomware, spyware, adware, and other malicious programs. Malware typically has one of the following objectives:
- Steal sensitive data such as login credentials, financial information, or personal information
- Encrypt files and hold them ransom until a payment is made (ransomware)
- Take control over a computer’s resources to create a botnet or mine cryptocurrency
- Generate fraudulent ad revenue through click fraud schemes
- Sabotage hardware, software, or networks
Malware is often spread through phishing emails, compromised websites, infected USB drives, and other vectors. Once a device is infected, malware can cause significant damage or be used as an entry point to breach entire corporate networks.
How do malware attacks happen?
There are several common infection vectors through which malware spreads:
- Email phishing – Malicious email attachments or links can install malware when opened by recipients.
- Infected websites – Visiting compromised sites can trigger drive-by downloads of malware.
- Malvertising – Clicking on tainted ads can infect devices with malware.
- Social engineering – Attackers trick users into installing malware by disguising it as legitimate software.
- USB drives – Portable drives spreading malware are left in public places in hopes people plug them in.
- Supply chain attacks – Software, hardware, or services from third-parties contain hidden malware.
Once a device is infected, the malware payload activates to achieve its objectives. This may involve stealing data, encrypting files for ransom, disabling security tools, or downloading additional malicious modules. The malware then tries to spread to other systems on the network or Internet to maximize damage.
Best practices for preventing malware
A multi-layered defense is required to protect against malware. Here are some best practices that individuals and organizations should follow:
Security awareness training
Educating employees and users on malware risks through security awareness training can limit infections. Topics to cover include:
- Identifying phishing emails and avoiding suspicious links/attachments
- Using strong passwords and multi-factor authentication
- Installing software only from trusted sources
- Thinking carefully before plugging in USB drives
- Reporting indicators of compromise or infection
Frequent security awareness training ensures users have up-to-date knowledge to avoid falling victim to malware.
Antivirus and anti-malware tools
Installing antivirus and anti-malware endpoint protection on all systems provides proactive scanning and monitoring to detect and block malware threats. Solutions should include features like:
- Real-time scanning of disk drives, memory, network traffic, etc.
- Heuristic analysis to identify suspicious behaviors and attributes
- Signature-based detection using constantly updated threat databases
- Sandboxing to safely test and analyze potential malware
- Remediation abilities to quarantine/remove infections
Enterprise antivirus consoles allow monitoring and managing all endpoints centrally. Keeping software updated is critical for detecting emerging and evasive malware strains.
Firewall and IPS devices
Network-level security devices provide additional inspection points to catch malware. Firewalls filter traffic and block communications with known malicious sites/infrastructure. Intrusion prevention systems (IPS) scan traffic patterns for indicators of compromise and can halt malware communication and payloads.
Patch management
Promptly patching software vulnerabilities prevents malware from exploiting them to infect systems and spread. Automated patch deployment for operating systems and applications ensures everyone is up-to-date.
Access controls and segmentation
Limiting user access rights to systems/data and segmenting networks serves to contain malware from easily moving laterally if infections occur. Multi-factor authentication also reduces unauthorized access that could facilitate malware activity.
Incident response planning
Having an incident response plan detailing the steps to rapidly detect infections, contain impact, eradicate malware, and recover systems allows organizations to minimize damage from malware incidents.
Backups
Maintaining recent backups of critical data denies malware like ransomware the leverage to extort organizations if files get encrypted.
Threat intelligence
Leveraging threat intelligence on active malware campaigns, adversary infrastructure, phishing lures, and other indicators allows proactive blocking of emerging malware attacks.
Common malware threats
Some examples of today’s most prevalent and dangerous malware threats include:
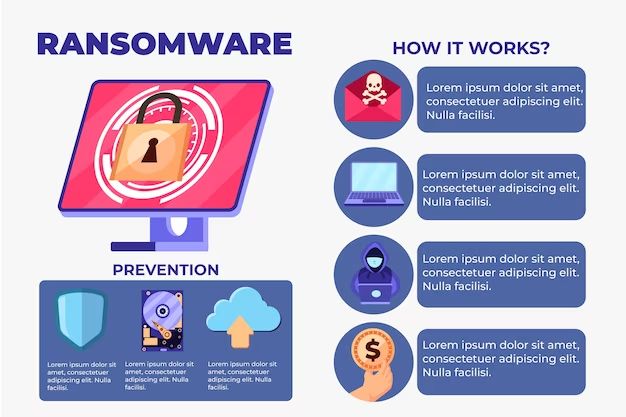
Ransomware
Ransomware encrypts files and demands payment for decryption keys. Recent strains like Ryuk, Conti, and Black Basta often target businesses and government agencies. Ransomware can cause massive disruption by making critical data inaccessible.
Trojans
Trojans disguise themselves as legitimate software while enabling backdoor access and control over the infected system. The Emotet and TrickBot trojans are used to steal banking credentials and spread other malware.
Spyware
Spyware secretly monitors computing activities and collects information like keystrokes, screenshots, emails, and browser history without consent. Predatory spyware stalkerware apps are used by domestic abusers.
Cryptominers
Cryptomining malware hijacks resources to mine cryptocurrency. Widespread cryptomining botnets like Pacha and Claymore have consumed massive amounts of computing power.
Botnets
Botnets comprise networks of malware-infected computers controlled by threat actors. Botnets can be leveraged to conduct DDoS attacks, spam campaigns, and other criminal activities.
Banking Trojans
Banking trojans steal login credentials and other information to conduct fraudulent wire transfers and drain accounts. The TrickBot and ZeusPanda banking trojans primarily target corporate bank accounts.
Backdoors
Backdoors allow remote access, control, and code execution on infected systems via command and control channels. APT groups install customized backdoors like Tunna and PAS to maintain long-term presence on high-value targets.
Mobile malware
As work and personal life blend on mobile devices, Android malware threats like xHelper, GriftHorse, and FluBot steal contacts, SMS messages, photos, and bank account information from mobile users.
Malware defense best practices for organizations
In addition to the general malware prevention measures outlined earlier, organizations can take further actions to protect themselves against advanced and targeted malware campaigns:
- Implement a Secure Email Gateway to filter out phishing emails and malware
- Use Domain-based Message Authentication, Reporting and Conformance (DMARC) to detect email spoofing
- Deploy web proxies and filtering to block malicious websites
- Enable DNS filtering to stop connections to known bad domains
- Use advanced endpoint detection and response (EDR) tools
- Conduct penetration testing and red team exercises
- Monitor for abnormal network traffic patterns and behaviors
- Hunt for indicators of compromise across systems
Taking a defense-in-depth approach reduces an organization’s attack surface and increases resilience against malware that gets past perimeter defenses.
Malware trends and future outlook
Malware continues to plague consumers and businesses worldwide, constantly evolving to develop new ways of infecting systems and evading security measures. Here are some key malware trends to expect in the near future:
- Increasing use of artificial intelligence to automate and scale attacks
- Targeting of cloud environments and supply chain vulnerabilities
- Leveraging social media networks and messaging apps to spread
- Growth of malware-as-a-service business model
- More ransomware targeting industrial control systems and IoT
- Continued mobile malware focus on stealing personal and financial data
With malware threats growing in frequency and sophistication, both individuals and organizations must remain vigilant by continually educating themselves, updating defenses, and adopting emerging technologies like AI-powered cybersecurity.
Protecting home computers and devices
Individuals and families connecting multiple devices in their homes face elevated malware risks. Here are tips for securing home computers and gadgets:
- Use antivirus/internet security suites on all computers and laptops
- Only download apps from official app stores like Apple App Store and Google Play Store
- Ensure all devices run the latest software versions
- Disable sideloading to block apps from unofficial sources
- Avoid clicking on links and attachments in unsolicited emails
- Backup critical data regularly in case of infection
- Use strong Wi-Fi encryption and firewalls to secure the network
- Enable personal hotspot security features if using phone tethering
Being selective about what is installed, avoiding suspicious downloads, and keeping everything updated greatly minimizes the malware risk for personal devices.
Conclusion
Malware represents one of the most significant cybersecurity threats facing our increasingly interconnected world. Preventing malware requires vigilance in identifying risks, educating users, deploying layered defenses, responding effectively to incidents, and adapting to an ever-evolving threat landscape. With malware attacks growing in scale and sophistication, organizations must make malware prevention a top priority to protect their data, systems, operations, and reputations into the future.