How to Keep Your Data Safe has become an increasingly pressing question for all of us in the digital age. As our personal and professional activities have moved online, the amount of sensitive data we generate, share and rely upon has exploded. Financial records, medical information, proprietary business data, confidential communications – safeguarding the privacy and integrity of our expanding digital footprint is critical.
Unfortunately, data threats have also grown increasingly sophisticated and aggressive. We face everything from individual cybercriminals stealing identities to state-sponsored hackers pursuing intellectual property to disgruntled insiders deleting records. Data breaches can mean immense financial losses, legal liabilities, compromised privacy and lasting reputational damages.
The good news is that with the right approach, you can implement robust protections to lock down your data tightly. While no single method is foolproof, adopting layered security across accounts, devices, services, networks and company policies can keep you resilient in the face of most attacks. Maintenance of sound backups provides insurance as well.
In this guide, we’ll explore in practical detail the essential strategies and best practices anyone can employ to maintain data security in the modern era. You’ll learn how to establish strong passwords, enable multi-factor authentication, identify phishing attempts, encrypt sensitive information, keep software patched and much more. Follow these tips to confidently utilize the digital world while keeping your valuable data safe from harm. Let’s dive in!
Understanding Data Security
Data security refers broadly to the protection of any confidential, proprietary, or sensitive information stored digitally from unauthorized access, theft, corruption, or deletion. Effective data security measures safeguard both data “at rest” in databases, files, and other repositories, as well as data “in motion” as it travels over networks and connections.
For individuals, personal data requiring security may include financial account credentials and payment card details, government identification numbers, medical/health records, emails, text messages, family photos and videos, and various document files containing private information. Individuals also generate sensitive data through their usage of modern apps, sites and devices which can potentially be exploited if not properly safeguarded.
For businesses, critical data requiring security spans a vast array of internal information such as customer/client personally identifying information (PII), employee records, intellectual property like patented designs or proprietary source code, confidential corporate documents, financial reports, transactional records, and operational data powering core systems. Breaches here can lead to identity theft, financial fraud, intellectual property theft, and disruption of normal operations.
Importance of Data Security
With increasing reliance on digital data storage and connectivity, ensuring robust security protections for sensitive data has become extremely important for several key reasons:
- Privacy – Keeping personal identities, behaviors, preferences, photos, messages, location history, and relationships private and away from unintended eyes.
- Compliance – Meeting legal and regulatory data protection, privacy and disclosure requirements which vary by jurisdiction and industry.
- Trust – Maintaining customer/partner trust by being a faithful steward of any data shared with your organization.
- Integrity – Preserving accuracy and completeness of data like financial records, medical info, or product designs.
- Continuity – Minimizing disruptions to core operations that depend on access to operational data and systems.
- Risk Mitigation – Reducing exposure to financial penalties, legal liabilities, intellectual property theft, and reputational damage from data incidents.
Given the potential scale of these repercussions, it is essential for both individuals and organizations to take their data security responsibilities seriously.
Types of Data Threats
While the specific techniques used are constantly evolving, common data security threats include:
- Malware – Viruses, ransomware, spyware, and trojans can infiltrate networks, computers, phones, websites, and apps leading to data theft or deletion.
- Phishing – Deceptive emails or sites masquerading as trusted sources to trick users into revealing credentials or downloading malware.
- Social Engineering – Manipulating or tricking authorized individuals to gain access to systems and data.
- Web App/API Attacks – Exploiting vulnerabilities in web/mobile apps and APIs to breach backend data sources they interact with. SQL injection is one example.
- Denial of Service (DoS) – Flooding sites and servers with excess traffic to make them crash and disrupt availability of data and systems.
- Data Interception – Tools like packet sniffers tap into unencrypted traffic on public networks to capture data and communications in transit.
- Unauthorized Access – Data breach through compromised or stolen login credentials or brute force hacking of insecure systems. Insider threats are also a risk.
- Physical Theft – Stealing computers, mobiles, storage media, or paper documents containing sensitive data.
- System Breaches – Compromising any part of the technology stack from the OS up through apps to gain data access.
With broad threats like these, multi-layered security defenses are necessary for comprehensive protection.
Establishing Strong Passwords
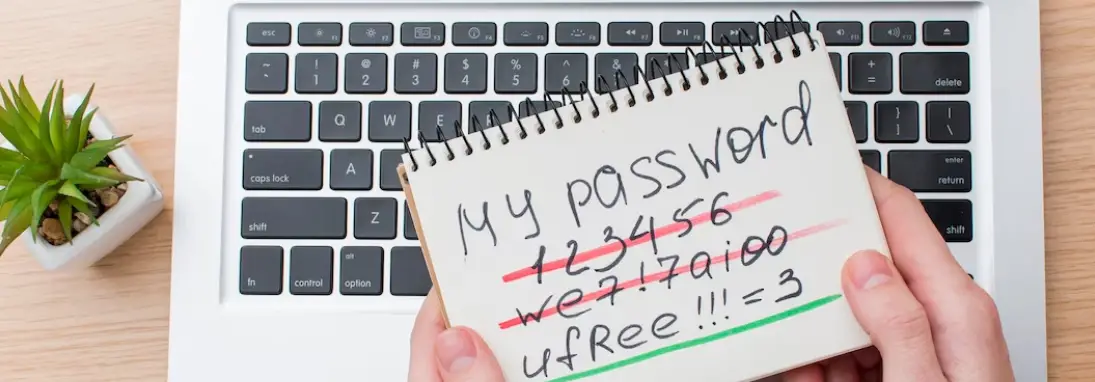
Having unique, complex passwords for every account and system is a fundamental data protection. Strong passwords create a critical first barrier against unauthorized access via hacking or stolen credentials. To enable robust password security:
- Use 8+ character passwords with upper/lowercase letters, numbers and symbols. Avoid common words.
- Avoid reusing passwords across different accounts or systems. Compromise of one leads to compromise of all.
- Consider using a password manager tool to securely generate and store unique passwords for all accounts.
- Change passwords periodically and immediately if credentials are ever compromised or suspected of being.
- Never share passwords openly via email or other unsecured channels.
- For high-value accounts, consider using passphrases of 12+ words/characters for very high security.
Adopting broadly strong password practices across the board thwarts the most common initial entry point for data breaches.
Implementing Two-Factor Authentication
Two-factor authentication (2FA) provides another layer of account security on top of passwords by requiring users prove identity through two mechanisms: 1) Something you know (the password) 2) Something you have (a generated code from an authenticator app or sent via SMS).
2FA should be enabled on any account supporting it, especially email, financial/payment accounts, health portals, government logins, or company systems containing sensitive data. Doing so greatly reduces the risk of stolen credentials being usable by attackers.
Popular 2FA apps like Authy or Google Authenticator generate time-sensitive codes offline. For ease of use, these are preferable over SMS codes which can have security limitations. 2FA adds just a few seconds to login while dramatically strengthening account security against compromise.
Using Secure Networks
In our increasingly mobile, interconnected world, ensuring you only access and transmit sensitive data over secured networks is key for preventing interception or “eavesdropping” of your information.
Public vs Private Networks
Due to the huge risks, public Wi-Fi networks at coffee shops, hotels, airports and other venues should generally be avoided for accessing or entering any sensitive personal/work data which could potentially be snooped on over the shared connection. For any confidential browsing or transactions, only known private networks with login protections should be used if public Wi-Fi is your only option.
Virtual Private Networks (VPNs)
When using public networks, a VPN (Virtual Private Network) establishes an encrypted tunnel from your device through the internet to a private server, hiding your web traffic and online activities from other network users. VPNs thus provide a secured connection for safe browsing and data access from any location.
Leading VPN providers like ExpressVPN and NordVPN offer user-friendly apps for computers and mobile devices, providing reliable security when you must use an open or unsecured network.
H2 Regular Data Backups
No data security plan is complete without regular, redundant data backups. Backing up copies of important files, documents, databases, and system configurations provides critical protection against data loss scenarios like:
- Ransomware that encrypts/deletes data
- Storage device failures
- Accidental deletions or corruptions
- Natural disasters, fires or floods
- Physical theft of computers or drives
Ideally, backups should be automated to run daily, with files saved to multiple locations for redundancy. This includes remote cloud backups to guard against physical damage. Test restorations regularly to ensure backups are viable.
With robust backup processes in place, breaches and data losses become far less catastrophic. You can restore compromised systems using uninfected backups once threats are neutralized.

Keeping Software Updated
Regular System Updates
Continually keeping operating systems, applications, firmware, databases and other system software updated with the latest vendor patches is imperative for closing security holes. Hackers aggressively seek to exploit known unpatched software vulnerabilities as entry points into systems and data.
To avoid this, ensure any systems you use for accessing, storing or transmitting sensitive data have automatic update features enabled wherever possible. This applies to computers, phones, apps, cloud services, networks, IoT devices and more. Make patching high priority and rapidly address any overdue updates.
Antivirus Software Updates
Similarly, reliable antivirus software should be run on all computers and laptops to detect and disable malware including viruses, trojans, spyware and ransomware which all threaten data security in different ways. Check that virus definitions are automatically updated daily so your scans catch the latest risks. Conduct full antivirus scans at least weekly.
Keeping software continuously updated is one of the most effective ways to prevent your systems from becoming vulnerable data targets.
Encrypting Sensitive Data
Encrypting data – scrambling it into unreadable code – ensures that only those with the secret decryption key can access the information, even if encrypted files or transmissions fall into malicious hands. Encryption should be applied to:
- Files containing highly sensitive info like customer PII, intellectual property, HR data, mergers and acquisitions
- Entire hard drives using full disk encryption to protect device theft
- Web and application traffic transmitted over networks, using TLS/SSL protocols
- Private email and messaging data
- Databases containing confidential data
Properly encrypted data is practically impossible to crack without the decryption key. It forces attackers to compromise a system with valid credentials in order to access protected information in decrypted plaintext. This vastly raises the difficulty of successfully stealing data.
Beware of Phishing Scams
Phishing scams use deceptive emails, sites, ads or messages posing as trusted entities to trick recipients into revealing login credentials, financial data or downloading malware. Phishing is one of the top threats to personal and organizational data security today, often serving as the first domino in major breaches.
Practicing caution and awareness when interacting with anything asking you to submit personal/company data or click unusual links thwarts most schemes. Other tips include:
- Carefully inspect sender names/addresses for inaccuracies
- Verify legitimacy by contacting supposed sources separately
- Avoid clicking direct links. Navigate independently to any requested sites.
- Check for website HTTPS encryption and verify security certificates
- If in doubt, report the suspicious message to appropriate IT/security teams
Promoting a culture and mindset of healthy skepticism for evaluating any unsolicited communications requesting sensitive data or to complete suspicious actions helps keep phishing from succeeding.

Educating Yourself and Your Team
Perhaps most fundamentally, continually learning about and prioritizing data security for yourself and your organization or family is essential for staying secure in the long run.
Data Security Training
Seeking formal training opportunities, credentials, workshops and conferences to expand your data security, privacy and cyber risk knowledge pays dividends in recognizing and responding to evolving threats over time. Forward-thinking businesses make such continuing education a priority for both leadership and employees. For individuals, free online training resources can provide great self-education.
Staying Informed About Latest Threats
Beyond training, simply reading data security industry news, blogs, reports and updates from experts helps you stay attuned to new attack methods, vulnerabilities and best practices as they emerge. Signing up for email newsletters, podcasts and updates from trusted security sources makes this easy.
Promoting awareness and emphasis on security from the top-down establishes it as an indispensable cultural priority, rather than an afterthought. This pays massive dividends in protecting data.
Conclusion
In closing, robust data security is a multifaceted challenge that requires applying layered protections across systems, software, accounts, networks, data storage, backups, encryption and employee practices. But with the right combination of technologies, processes and training, both individuals and organizations can implement strong defenses to preserve the privacy and integrity of sensitive information against escalating threats. No single solution alone provides effective security – true resilience requires regularly assessing risks, monitoring the landscape, hardening vulnerabilities, and instilling vigilance and care at all levels in how data is handled. With proper understanding and smart precautions, you can be confident your data is safe from harm.
Frequently Asked Questions
What are some effective data security measures?
Some key data security best practices include using strong passwords, implementing multi-factor authentication, encrypting sensitive data, installing antivirus software, avoiding public WiFi for confidential browsing, enabling automatic software updates, performing regular backups, and being cautious against phishing attempts. Taking a layered, defense-in-depth approach to security is most effective.
How can I protect my privacy on social media?
To better protect your privacy on social media, be wary of sharing personal details publicly, lock down your privacy settings, limit friends/followers to only those you actually know, disable location tagging where not needed, and restrict ad targeting permissions. Also be selective in what photos, activities, and opinions you share publicly.
What are the best online privacy protection services?
Top online privacy services include virtual private networks (VPN) like ExpressVPN and NordVPN to encrypt browsing data, secure email providers like ProtonMail that offer end-to-end encryption, password managers such as LastPass for managing unique and complex passwords, and anti-tracking web browsers like DuckDuckGo that minimize data collection.
Why is it important to keep personal information private online?
Keeping personal data private online prevents identity theft, financial fraud, cyberstalking, and other harms. It protects details about your life, relationships, location, habits, beliefs, and more from being seen by unintended parties or misused by companies and criminals. Personal privacy is a fundamental right.
What are some ways to store data safely?
Safe data storage options include encrypting sensitive files and hard drives, using cloud storage services with robust security like Dropbox or iDrive, storing data on air-gapped backups not continuously connected to networks, protecting devices with passwords/biometrics, and physically securing external hard drives in locked locations.
How can I safeguard my account and protect my data?
Account safety best practices include unique strong passwords, multi-factor authentication everywhere possible, avoiding password reuse across sites, not clicking suspicious links, watching for phishing attempts, using privacy-focused online services when available, limiting personal data sharing, and monitoring accounts regularly for any suspicious activity.
What are the risks of using public WiFi?
Public WiFi poses risks because it allows others on the same open network to more easily intercept your browsing data and communications. Avoid accessing or entering sensitive personal and work data when using public WiFi. Use a VPN if you need secure access.
How can companies protect customer data?
Companies should encrypt stored customer data, anonymize it where possible, follow least privilege access policies, implement cybersecurity defenses like firewalls and intrusion detection, perform regular security audits, vet third party services, provide security training to employees, and have an incident response plan.
What is the best way to back up important data?
The best practice is to maintain automatic, redundant backups in multiple locations like external drives and the cloud. Back up regularly and test restores periodically. Ensure backups are encrypted, access-controlled, and include system images, files, databases, and configurations.
What are signs of a phishing email or message?
Phishing indicators include urgency, threatening language, odd senders, mismatched links, unusual requests, poor spelling/grammar, and generic greetings. Verify legitimacy through separate channels before clicking links or attachments. Report suspicious messages.
How can I keep my passwords secure?
Use a unique complex password for each account, change passwords periodically, avoid reusing passwords, use a password manager, don’t share passwords openly, and enable two-factor authentication where possible. Strong password security is fundamental.
What should I do if my data is compromised?
If accounts or personal data are compromised, immediately change passwords, enable extra security protections, monitor for suspicious activity, report the incident to relevant institutions, and review recent transactions and statements for signs of fraud. Move quickly to secure data.


