The Health Insurance Portability and Accountability Act (HIPAA) is a federal law that provides data privacy and security provisions for safeguarding medical information. HIPAA sets national standards for protecting the confidentiality, integrity and availability of electronic protected health information (ePHI).
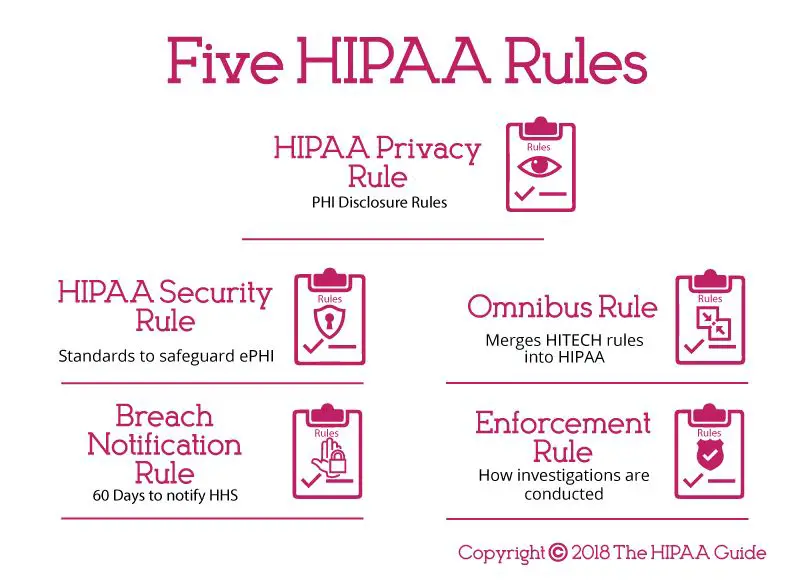
There are 5 core rules that make up the foundation of HIPAA compliance:
Rule 1: Notice of Privacy Practices
The first rule under HIPAA is the Notice of Privacy Practices (NPP). This is a document that healthcare organizations must provide to patients which explains how they will use and disclose the patient’s protected health information (PHI).
Some key elements of the NPP include:
- A header stating it is a Notice of Privacy Practices
- A description of how the provider may use and disclose PHI
- A summary of the patient’s health information rights
- The provider’s duties to protect privacy
- Contact information for questions or complaints
The NPP informs patients up front how their health data will be handled. It outlines what PHI will be collected, what it will be used for, with whom it may be shared and the safeguards in place to protect confidentiality.
This transparency allows patients to make an informed decision about whether to agree to treatment with the knowledge of how their information will be handled.
Key Facts on the NPP Rule
- Providers must make a good faith effort to obtain written acknowledgement from the patient that they received the NPP.
- The NPP must be provided at the first patient encounter.
- The NPP must also be posted prominently and made available upon request.
- If the NPP changes, a revised copy must be made available.
- If PHI is being used in a manner not described in the current NPP, the patient must be notified and given the opportunity to object.
Adhering to the NPP rule ensures patients understand their rights and how their PHI will be handled before agreeing to treatment.
Rule 2: Uses and Disclosures of PHI
The second rule under HIPAA establishes under what conditions PHI can be used and disclosed. PHI refers to all individually identifiable health information transmitted or maintained in any form or medium.
This rule essentially defines the lawful and permitted uses and disclosures of PHI. It also requires that reasonable safeguards are in place to limit incidental, and avoid prohibited, uses and disclosures.
Some examples of permitted uses and disclosures under HIPAA include:
- For treatment purposes – such as sending PHI to a specialist for a consultation
- For payment activities – such as submitting PHI on claim forms to collect payment from an insurer
- For healthcare operations – such as internal quality control and auditing
- When required by law and public health activities
- For victims of abuse, neglect or domestic violence
- For health oversight activities such as investigations or licensure reviews
- For judicial and administrative proceedings as required by a court order
- For law enforcement purposes under certain conditions
- For research studies that meet privacy requirements
- To avoid a serious threat to public health or safety
Prohibited disclosures include using or disclosing PHI for marketing purposes or any use or disclosure that violates state or other laws. Limited data sets used for research, public health or healthcare operations may exclude direct identifiers. Any other uses or disclosures not outlined under the permitted categories are also prohibited without written patient authorization.
HIPAA supports the flow of health information for patient care while limiting unnecessary access and distribution to protect privacy. The permitted uses relate to treatment, payment and healthcare operations.
Key Facts on the Use and Disclosure Rule
- PHI can only be used or disclosed for purposes not requiring written patient authorization if it falls under a permitted category in the law.
- Reasonable safeguards must protect against incidental uses and disclosures and limit them to the minimum necessary.
- Minimum necessary means limiting PHI access to only the information needed to accomplish the intended purpose.
- HIPAA does permit certain disclosures without patient authorization – to the patient directly, for directory purposes, and involving family and friends, among others.
- All other uses and disclosures not permitted by law require the patient’s written authorization
Limiting PHI uses and disclosures maintains patient privacy while allowing important health information to flow when truly needed for patient care and safety.
Rule 3: Patient Rights
The third rule under HIPAA gives patients specific rights over their health information. These ensure patients stay informed and in control of how their PHI is used.
HIPAA provides patients with the following health information rights:
- Access to records – Patients can access and obtain copies of their medical records and billing records from health plans and healthcare providers.
- Amendments – Patients can request an amendment to their PHI if they feel it is inaccurate or incomplete.
- Disclosures – Patients can request a list of who their PHI has been disclosed to, such as for treatment, payment or healthcare operations.
- Restrictions – Patients may request limits on how their provider uses or discloses PHI. The provider is not required to agree but, if they do, they must honor the restrictions.
- Confidential communications – Patients can ask to receive PHI communications from their provider by alternative means or locations if they believe additional privacy is needed.
- Breach notification – Patients have a right to be notified if there is a breach of their unsecured PHI.
- Copy of NPP – Patients can obtain a paper copy of the provider’s Notice of Privacy Practices.
Granting patients access and control over their PHI strengthens their ability to monitor how their health information is managed. It promotes transparency and engagement in healthcare.
Key Facts on HIPAA’s Patient Rights
- With limited exceptions, healthcare providers and health plans must comply with patient requests related to rights over their PHI.
- Providers have 30 days to respond to patient requests for access or restrictions, 60 days if needed.
- Providers can deny patient amendment requests if they believe the PHI is accurate and complete.
- Disclosure request responses must include PHI disclosures going back 6 years, with some exceptions.
- Reasonable requests for confidential communications must be accommodated.
- If patients pay for care out-of-pocket and request restriction on disclosure to their health plan, providers must comply.
HIPAA’s patient rights provisions uphold patient autonomy by enabling individuals to direct the sharing and use of their health information.
Rule 4: Administrative Requirements
The fourth rule under HIPAA establishes administrative requirements for healthcare providers and business associates to ensure they have the appropriate safeguards in place to protect PHI.
Some of the key administrative requirements include:
- Health providers and business associates must conduct risk analyses to identify vulnerabilities, implement safeguards and document their compliance efforts.
- Business associate agreements must be in place if the provider is engaging other entities that handle PHI. These agreements establish privacy and security responsibilities.
- Providers must designate a HIPAA compliance or privacy officer responsible for developing and implementing privacy policies.
- Staff must be trained on HIPAA regulations with procedures in place to prevent improper disclosures.
- Providers must apply physical and technical safeguards to protect data integrity, confidentiality and availability.
- INCIDENT RESPONSE PROCEDURES MUST BE DEVELOPED FOR MANAGING SECURITY BREACHES.
Proper administrative policies demonstrate a commitment to HIPAA compliance. They also support consistent implementation of safeguards for securing PHI across a healthcare organization.
Key Facts on HIPAA Administrative Requirements
- Documented risk analyses must be completed regularly and when systems or processes change.
- Business associate agreements establish liability for associates to handle data according to HIPAA rules.
- Staff training should be completed upon hire and when job responsibilities related to PHI change.
- Technical safeguards include access controls, encryption, audit logging and network protections.
- Physical safeguards range from facility access controls to device and media security policies.
- HIPAA requires administrative policies and procedures be documented and periodically updated.
Ongoing risk analyses, training programs, and policy updates help demonstrate an active commitment to HIPAA compliance.
Rule 5: Breach Notification Rule
The fifth rule under HIPAA establishes requirements for healthcare providers and business associates for notifying patients and the Department of Health and Human Services (HHS) in the event of a breach of unsecured protected health information.
Under HIPAA, a breach is unauthorized access, acquisition, use or disclosure of PHI that compromises the security or privacy of the information. Exceptions include unintentional access by employees or inadvertent disclosures with reasonable safeguards in place.
When a reportable breach occurs, the HIPAA breach notification rule requires:
- Patients must be notified without unreasonable delay, no later than 60 days after discovery.
- Notification must include details about the breach, types of information involved, steps affected individuals can take to protect themselves, and actions being taken to investigate and mitigate harm.
- HHS must be notified no later than 60 days after discovery for breaches impacting 500+ individuals.
- Breaches impacting under 500 individuals must be reported to HHS within 60 days of the end of the year.
- Business associates must notify covered entities of breaches without unreasonable delay and no later than 60 days after discovery.
Prompt notification and robust reporting enables patients to take action following unauthorized access to their PHI. It also supports federal health privacy oversight.
Key Facts on the HIPAA Breach Notification Rule
- All impermissible uses or disclosures of PHI are presumed to be breaches unless it can be demonstrated there is a low probability the PHI was compromised.
- Timely internal breach investigation and risk assessment must determine whether notification is required.
- HHS and media outlets may be notified by healthcare providers about large-scale breaches posing significant risk of financial, reputational or other harm to affected individuals.
- Penalties for non-compliance with breach notification requirements include civil monetary fines and, for willful neglect, criminal charges.
- Breach notifications must be made by first-class mail or email if specified as a preference. If insufficient or out-of-date contact information is available, substitutes like website postings may be used.
The transparency required around breaches motivates healthcare organizations to prioritize PHI security and swiftly respond to contain impacts of unauthorized data access.
Conclusion
HIPAA establishes consistent national standards through these 5 rules – the Privacy Rule, Security Rule, Breach Notification Rule, Enforcement Rule and Patient Rights Rule. Together they represent safeguards for managing protected health information in a digital world.
By providing patients with new rights over their data, limiting uses and disclosures, requiring administrative policies and technical controls, and mandating breach reporting, HIPAA strikes a balance between information privacy and permitted flows for treatment and other essential purposes.
Healthcare providers and their business associates are responsible for full compliance. Patients can file complaints with providers or HHS when HIPAA rights are violated.
Ultimately, robust HIPAA compliance demonstrates an organization-wide commitment to managing health data with integrity. In an era increasingly defined by technology, HIPAA’s ground rules still offer a trusted framework for handling sensitive patient information with care.