With the increasing use of digital technology in our daily lives, digital evidence is now a key component in many criminal investigations and legal proceedings. However, there are several unique problems that arise in trying to properly preserve digital evidence to maintain its integrity and admissibility in court. Understanding these challenges is crucial for law enforcement, legal teams, and cybersecurity professionals when handling digital evidence collection and preservation.
Ensuring Proper Collection and Acquisition
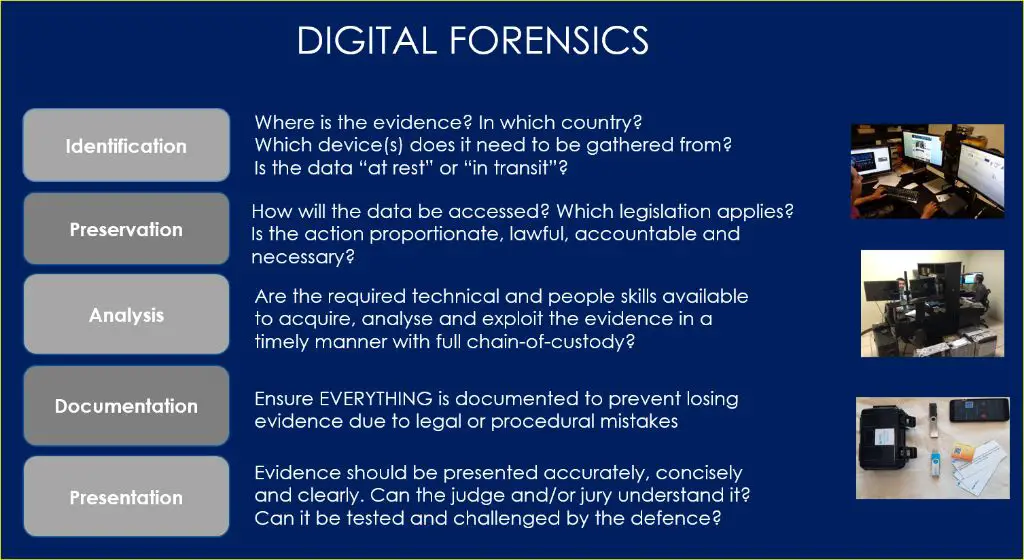
A core issue for preserving digital evidence is ensuring it is collected and acquired correctly at the start. Mishandling the initial collection can irreversibly damage the evidentiary value down the line. Some key challenges include:
- Using forensic software and hardware designed for evidence collection – Standard computers and devices can alter digital evidence files and metadata.
- Following strict procedures like write-blocking – Write-blocking prevents modifying data when connecting evidence drives and devices during acquisition.
- Collecting from volatile memory – Capturing system RAM contents before shutdown can provide crucial recent activity data.
- Avoiding contamination – Evidence drives should not be mounted onto examiner systems, only copies should be used.
- Documenting everything – Comprehensive logs must be kept on all collection steps, tools, settings, and personnel involved.
Without proper acquisition from the start, preserving digital evidence for court becomes nearly impossible. Training and resources are needed for proper evidence seizure and collection capabilities.
Maintaining a Chain of Custody
Closely tied to collection is maintaining a clean chain of custody – the ability to chronologically document everyone who handled evidence items. Lapses in the chain of custody can jeopardize the integrity and admissibility of digital evidence. Challenges include:
- Tracking all evidence movements – Detailed records must be kept on all transfers and reviews of copies.
- Using access controls – Physical and digital restrictions prevent unauthorized access.
- Proper transfer procedures – Following strict intake and release processes, including cryptographic hashing to validate file integrity.
- Limiting access only to copies – The original evidence should remain untouched if possible.
- Preventing contamination – Systems used to examine evidence cannot also be used for general activities.
Gaps in the chain of custody can damage the perceived reliability of digital evidence in legal contexts. This requires coordination between forensic teams, lawyers, and other staff to maintain clean records.
Preserving Data Integrity
A key aspect of preservation is ensuring the original integrity of digital evidence is maintained without alteration or data corruption over time. However, various technical and human factors make this difficult:
- Media degradation – Digital storage media can deteriorate, develop bad sectors, or fail entirely.
- File corruption – Improper shutdowns, connections, or programs can alter binary data.
- Metadata changes – Timestamps, access logs, and other metadata can easily be modified.
- Encryption – Encrypted data becomes inaccessible if passwords and keys are lost.
- Human error – Improper handling or accidental changes and deletions.
Organizations must implement robust digital preservation strategies like redundant backups, file integrity monitoring, write-blocking, and strong access controls to prevent evidence alteration.
Authenticating Evidence
Courts require affirming that any presented digital evidence is authentic and has not been manipulated or falsified. This can be challenging with electronic files:
- Establishing definitive authorship – It can be difficult to prove who created or modified specific digital files.
- Detecting edits – Digital metadata like timestamps can be modified to hide edits.
- Proving completeness – It is often impossible to validate if file contents are complete or if data is missing.
- Confirming origin – The original source system of digital evidence is not always definite.
Overcoming these authentication challenges requires technical capabilities like cryptographic hashing and detailed logs. But testimony on collection practices and the full chain of custody also plays a major role in evidence admission.
Accessibility and Formats
Digital evidence risks becoming inaccessible in the future as technologies, computing platforms, and file formats change. Challenges include:
- Legacy media – Old disks, drives, and various media can become unreadable as the equipment to access them disappears.
- Outdated formats – Software and hardware needed to open obsolete files and formats ceases to exist or work.
- Proprietary systems – Evidence in proprietary systems with no export options have accessibility issues long-term.
- Encryption – Encrypted data is unrecoverable if the keys are lost, no matter the format.
- Bit rot – Slow decay of magnetic storage results in flipped bits and corruption.
Maintaining long-term accessibility requires migrating evidence to new formats and storage media. But this risks altering the data, so originals must also remain untouched.
Picking Appropriate Preservation Formats
To balance accessibility and integrity, evidence files must be stored in formats that remain readable in the future but avoid changes to the data. This requires carefully choosing standards-based, non-proprietary formats like:
- Images – TIFF, PNG for raster images; SVG for vector.
- Documents – PDF/A for documents; OpenDocument for office files.
- Audio/video – FLAC for audio; MKV for video.
- Archives – TAR for efficient archiving without compression.
Proprietary formats like JPG, DOC, and MP3 should be avoided for evidence preservation if possible. Formats should also avoid compression which alters file contents. But proprietary formats may still hold value as secondary copies if the original format is preserved.
Ensuring Long-Term Storage and Viability
Another fundamental issue for preserving digital evidence is planning storage locations and systems that remain reliably accessible for timespans of years or decades. This requires considering:
- Media lifespan – Optical discs and specialized flash media offer longer lifespans than hard drives.
- Geographic distribution – Storing copies in multiple physical locations mitigates localized risks.
- Maintenance procedures – Workflows for periodically checking and copying to new media as needed.
- Redundancy – Maintaining multiple copies and checksums to avoid data loss.
- Resources – Allocating sufficient staff and IT infrastructure for ongoing management and security.
Due to high long-term costs, many organizations unfortunately take shortcuts that put evidence integrity and accessibility at risk over time.
Security and Access Management
Digital evidence must be strongly protected against unauthorized access, tampering, or leaks that compromise investigations and court cases. Challenges include:
- Least privilege – Only individuals with a direct need should have file access.
- Encryption – Encrypted files provide additional protection if access controls fail.
- Tracking access – Detailed audit logs should record all file and system access.
- Network isolation – Systems should not connect to any networks where possible.
- Physical security – Storing media in locked, monitored rooms guards against theft.
However, excessive restrictions can also obstruct legitimate case examination and discovery requests. Balancing access control with availability is difficult.
Navigating Legal Requirements and Obligations
Preserving digital evidence must account for various legal requirements that can conflict with limited available resources:
- Retention periods – Evidence may need preservation for months or years based on statutes.
- Disclosure obligations – All relevant evidence must be accessible for legal discovery.
- Admissibility rules – Following jurisdictional guidelines to ensure court acceptance.
- Data privacy – Laws like HIPAA govern information sharing and redaction.
- Exponential growth – More cases and data makes costs quickly unsustainable.
Better legal guidelines tailored to digital evidence are needed. But currently, trade-offs between obligations and practicality are often inevitable.
Lack of Training and Specialized Skills
Working with digital evidence is a highly specialized skillset, but many organizations lack staff with the necessary training. Key personnel gaps include:
- Forensics specialists – Proficiency in collection tools, procedures, and operating systems.
- Data analysts – Ability to reconstruct fragmented data and timelines.
- Records managers – Knowledge on evidence tracking and information governance policies.
- Legal expertise – Understanding rules of evidence and admissibility.
- IT infrastructure – Engineers to build secure storage systems and networks.
Filling these skill gaps requires recruiting, partnerships with vendors, and better digital forensics training programs.
Conclusion
From collection through long-term preservation, organizations face immense challenges managing and safeguarding digital evidence. Lacking proper training, tools, resources,formats, infrastructure, and planning puts evidence integrity, accessibility, and admissibility at risk. While improving, technology and policies are still playing catch-up in the digital age. But progress can be made through education, standards, redundancy, specialized tools, and better alignment between IT, legal, forensic, and records management teams. With digital evidence now central to so many investigations and cases, developing strong preservation strategies is fundamental to justice.